Opening (and subsequently bricking) a pfSense SG-2440 to replace a Dell Optiplex 755 stacked with network cards to run as firewall:


Well dang, I bricked my new firewall by attempting to restore the full XML configuration from the old firewall. I had to kick over into UART access via USB:
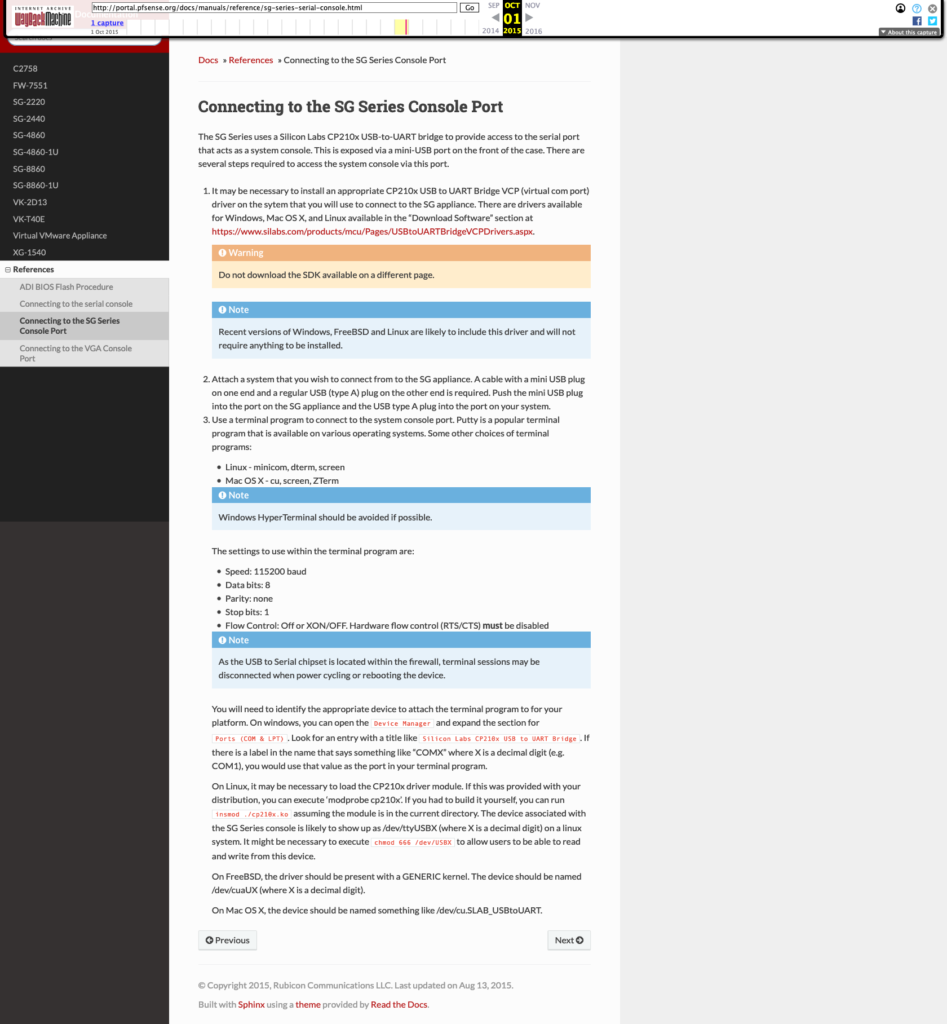
2020 update: The Netgate article that I originally linked to now redirects to a login form. You can use this Internet Archive link to access the older documentation.
2017 update: in the time since I wrote this article, a friend recommended Serial, which allows me to access the serial port without the need for virtualization of Linux.
I used Ubuntu Linux that I run under VMWare Fusion (I don’t want to add on a bunch of kernel drivers that will probably become outdated/abandoned as OS X progresses). After wasting a chunk of amount of time on minicom, I switched over to GNU Screen, which worked like a champ (as always) using the following:
sudo screen /dev/ttyUSB0 115200 8N1,-ixoff,-ixon
Y.M.M.V. for what your /dev/ address is, but tailing your kernel/dmesg logs and/or dorking around with lsub should hopefully help you find it.



Since the system doesn’t even boot pfSense (F1), then I’m going to have to use Andre LaBranche’s guide “Nuke and pave of pfSense on the SG-2440” for flashing from a USB stick, and will spend more time on that tomorrow.
The biggest difference between his guide for OS X and my use on Ubuntu 14 (running under VMWare Fusion on an OS X system) are:
- As I mentioned in my prior entry, I used GNU Screen to connect. If you need to find out the device’s /dev/ path for using with GNU Screen, try using this solution found on Stack Exchange.
- Instead of
gzcat(which wasn’t available), I usedzcat, though you can also usegunzip -c file.tgz.



Once I have my SG-2440 back up and running after a flash, the next few challenges will be to reconfigure most everything by hand, and either sifting through (and/or trying to craft my own) XML restore file, or going screen-by-screen in comparison to old and new firewall implementations. This doesn’t excite me in the slightest. :’-(
It would be nice to have the NanoBSD install of pfSense in place of the “full install”, but that will probably reduce my options (e.g. packages) and most everyone keeps their firewalls on a UPS anyways, so then the question is more over into how to tie it to the UPS and feed the UPS power data to other portions of the network that should know the status (e.g. using MQTT), and also have the ability to power back up even if there is a catastrophic interruption (e.g. using Z-Wave).
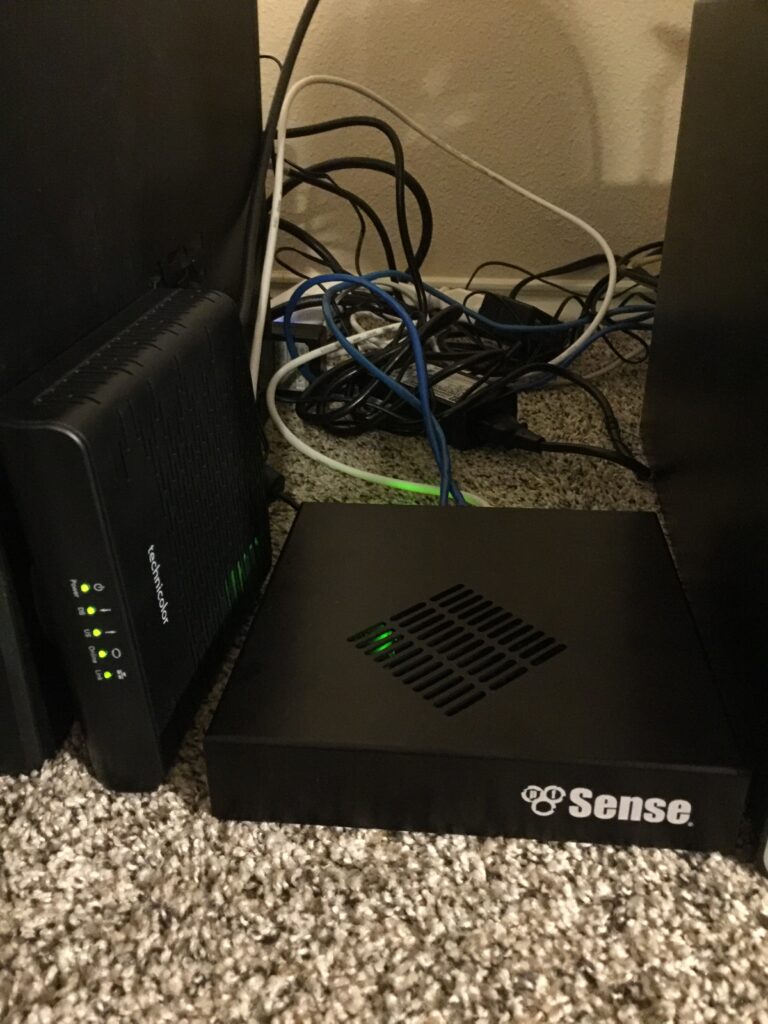
Now the firewall is working again, and I can focus on cable management:
Did this article save you time or money? I'd love a coffee!
Did you find this useful?
Please share with those who you believe would find this useful too!
